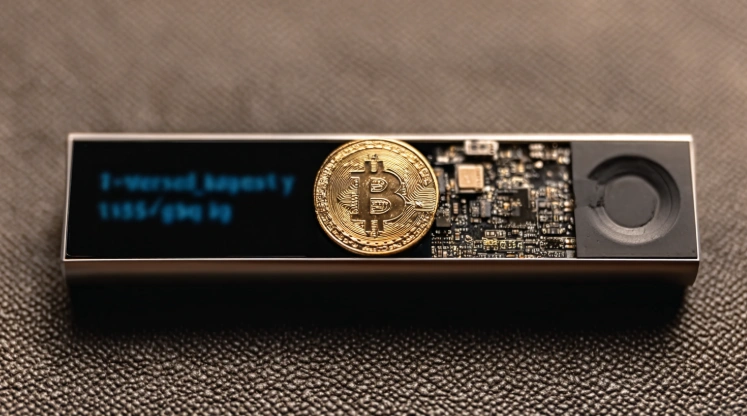
Ledger Bitcoin Recovery: Identifying and Correcting Security Mistakes
Ledger Bitcoin Recovery necessity often results from BTC wallet errors that users inadvertently introduce through improper security practices requiring correction before consequences occur. The user security mistakes category encompasses preventable vulnerabilities that transform secure cold storage into compromised holdings. Understanding common mistakes enables identification and correction protecting private keys before loss occurs.
Security mistakes accumulate over time as users develop convenient but dangerous habits. Many errors seem harmless individually but create cascading vulnerabilities when combined. Systematic security review identifies and corrects mistakes restoring proper hardware wallet protection.
This mistake analysis covers phrase mismanagement, update neglect, credential weakness, digital exposure, and recovery verification for complete crypto security across all supported coins via USB-C or Bluetooth connection.
Seed Phrase Mismanagement
Seed Phrase Mismanagement represents critical BTC wallet errors in backup handling creating Ledger Bitcoin Recovery vulnerabilities through compromised protection. The incorrect storage scenario addresses improper backup methods while single copy covers insufficient redundancy. Identifying mismanagement enables user security mistakes correction for private keys safety.
Phrase handling errors represent most consequential mistakes for cold wallet security.
Incorrect Storage
Incorrect storage methodology errors:
| Storage Method | Risk | Correction |
|---|
| Desk drawer | Discovery | Move to safe |
| Wallet pocket | Loss/theft | Relocate securely |
| Unlabeled paper | Confusion | Clear labeling |
| Fading ink | Illegibility | Metal plate |
| Humid environment | Degradation | Climate control |
| Near electronics | EMF exposure | Isolated storage |
Incorrect storage creates BTC wallet errors requiring immediate correction. The Ledger Bitcoin Recovery prevention depends on proper storage for private keys via USB-C across all supported coins.
Single Copy
Single copy redundancy failure:
- Single copy creates total loss risk
- Any damage eliminates recovery capability
- Theft of single copy means permanent loss
- Fire destroys unprotected single backup
- Water damage renders paper illegible
- Misplacement of single copy catastrophic
- Single location vulnerability extreme
Single copy represents critical user security mistakes requiring multiple backup creation. The hardware wallet phrase requires redundancy for cold storage via USB-C unlike Trezor or KeepKey single copy risks across all supported coins.
Ignoring Firmware Updates
Ignoring Firmware Updates creates BTC wallet errors through software currency neglect affecting Ledger Bitcoin Recovery security posture. The outdated Ledger scenario addresses version neglect while security vulnerabilities covers protection gaps. Update compliance corrects user security mistakes for crypto security.
Firmware currency affects both security and functionality for cold wallet operations.
Outdated Ledger
Outdated Ledger version neglect. Update compliance procedure:
- Connect device to Ledger Live
- Navigate to My Ledger section
- View current firmware version
- Check for available updates
- Read release notes carefully
- Click install if available
- Wait for completion fully
- Verify genuine check passes
- Test device functionality
- Document update completion
Outdated Ledger represents BTC wallet errors from version neglect. The Ledger Bitcoin Recovery security depends on current firmware for private keys via USB-C.
Security Vulnerabilities
Security vulnerabilities protection gaps:
| Gap Type | Risk Level | Correction |
|---|
| Unpatched exploit | Critical | Update immediately |
| Old cryptography | High | Firmware update |
| Feature absence | Medium | Version upgrade |
| Compatibility issue | Medium | Stay current |
| Support limitation | Low | Maintain currency |
Security vulnerabilities create user security mistakes through protection gaps. The hardware wallet update compliance ensures cold storage via USB-C or Bluetooth across all supported coins.
Weak PINs and Passphrases
Weak PINs and Passphrases represent BTC wallet errors through inadequate access control enabling Ledger Bitcoin Recovery bypass scenarios. The easy to guess pattern addresses predictability while reused passwords covers credential overlap. Credential strengthening corrects user security mistakes for private keys protection.
Access control weakness enables unauthorized device use for cold wallet compromise.
Easy to Guess
Easy to guess predictable credentials:
- Sequential numbers (123456)
- Repeated digits (000000)
- Birth dates (personal connection)
- Phone numbers (discoverable)
- Common patterns (147258)
- Previous PINs (possibly known)
- Simple progressions (111222)
Easy to guess credentials create BTC wallet errors through predictability. The Ledger Bitcoin Recovery prevention requires random credentials for private keys via USB-C.
Reused Passwords
Reused passwords credential overlap dangers:
| Overlap Type | Risk | Correction |
|---|
| Same PIN everywhere | Total exposure | Unique device PIN |
| Passphrase reuse | Database breach | Unique passphrase |
| Pattern similarity | Easy guessing | Random selection |
| Shared credentials | Known to others | Private only |
Reused passwords represents user security mistakes enabling unauthorized access. The hardware wallet requires unique credentials for cold storage via USB-C unlike Trezor or KeepKey PIN policies across all supported coins.
Digital Exposure
Digital Exposure creates critical BTC wallet errors through electronic phrase storage enabling Ledger Bitcoin Recovery compromise scenarios. The photos of seed addresses image-based exposure while cloud backups covers remote storage risks. Eliminating digital exposure corrects user security mistakes for crypto security.
Digital storage represents highest-risk mistake category for cold wallet compromise.
Photos of Seed
Photos of seed image exposure correction:
- Delete all phrase photographs immediately
- Remove from recently deleted folders
- Check cloud photo services for sync
- Verify backup services for copies
- Review device backup contents
- Clear image recognition caches
- Document deletion completion
Photos of seed represents critical BTC wallet errors requiring immediate correction. The Ledger Bitcoin Recovery prevention requires image elimination for private keys via USB-C.
Cloud Backups
Cloud backups remote storage elimination. Cleanup procedure:
- Identify all cloud storage services
- Search for phrase-related content
- Delete from all locations found
- Empty trash and recycling
- Revoke app access permissions
- Review automatic backup settings
- Exclude sensitive content paths
- Verify complete removal
- Create physical-only replacement
- Document cleanup completion
Cloud backups represents user security mistakes through remote exposure. The hardware wallet phrase requires physical-only storage for cold storage via USB-C or Bluetooth across all supported coins.
Recovery Check
Recovery Check validates correction effectiveness for Ledger Bitcoin Recovery through BTC wallet errors verification after security improvements. The test restoration process confirms backup accuracy while verify balances validates complete access. Verification confirms user security mistakes correction success for crypto security.
Verification confirms improvements effective for cold wallet assurance.
Test Restoration
Test restoration correction verification:
| Test Type | Method | Success Indicator |
|---|
| Recovery Check | Ledger Live feature | Green confirmation |
| Secondary device | Full restore | Accounts appear |
| Balance check | Account review | Values correct |
| Transaction test | Small transfer | Successful completion |
Test restoration confirms BTC wallet errors correction effectiveness. The Ledger Bitcoin Recovery capability verification protects private keys via USB-C across all supported coins.
Verify Balances
Verify balances complete access confirmation:
- Check all expected accounts display
- Compare balances to prior records
- Verify transaction history complete
- Test small send capability
- Confirm receive address generation
- Document verification completion
- Schedule periodic re-verification
Verify balances confirms user security mistakes correction through functional testing. The hardware wallet complete access ensures cold storage via USB-C or Bluetooth unlike Trezor or KeepKey balance verification across all supported coins.
For secure setup, see our Secure Your Ledger Bitcoin Wallet. For prevention strategies, visit Ledger Recovery Prevention Strategies.
Frequently Asked Questions
What is the most common Ledger security mistake?
Storing recovery phrase digitally through photos, cloud backup, or text files. Creates multiple exposure vectors. Physical-only storage eliminates this critical vulnerability.
How do I fix single copy backup mistake?
Create additional copies immediately using durable materials. Store in separate physical locations. Verify each copy accuracy. Maintain equal security attention.
Why are sequential PINs dangerous?
Easily guessed through simple attempts. Provide minimal brute force resistance. Random 6-8 digit PINs provide significantly stronger protection.
Should I delete old phrase photos immediately?
Yes. Delete from all locations including cloud services, backups, and recently deleted folders. Verify complete removal. Create physical-only replacement backup.
How do I verify my security improvements worked?
Use Recovery Check for backup validation. Test functionality through small transaction. Verify all accounts display correctly. Document verification completion.
Can outdated firmware cause security problems?
Yes. Outdated firmware may have known vulnerabilities. Security patches address discovered issues. Update monthly minimum for current protection.
What if I cannot correct all mistakes immediately?
Prioritize digital exposure elimination first. Then address PIN weakness. Create additional backups. Update firmware. Systematic correction over time acceptable.